10 Best Practices for Secure Online Payment Processing
9 min read
•
18 Jan 2023
The world of payments is shifting, with a greater focus on digital payment methods than ever before. While that has enabled the growth of ecommerce, it’s also created more opportunities for fraudulent activity.
As a business owner, you know the importance of providing safe, secure transactions for your customers. Without proper measures in place, you risk losing business as well as facing major fees and financial issues. Thankfully, there are plenty of tools at your disposal to ensure your business can provide secure online payment processing. Read on to learn more.
{{text-box}}
10 Best Practices for Secure Online Payment Processing
1. Tokenize and Encrypt Data
Tokenization and encryption are two critical tools for safeguarding sensitive information. With tokenization, credit card data is replaced with a randomized set of numbers (a token). The payment system replaces the details with a different token for every transaction, so even if someone shops with you twice, they’ll get a different token each time.
The token isn’t related to the customer’s private information. So, even if a hacker did somehow get into the servers, there would be no card details to steal.
Encryption is a great tool for storing or moving data. The system encrypts data and turns it into unreadable text (ciphertext). Only the receiver with the proper encryption key can access the hidden information.
2. Use 3D Secure 2.0
3D Secure 2.0 (3DS2) is an authentication method that helps ensure that the person you’re selling to is a legitimate customer. Pay.com supports 3DS2 because it adds an additional layer of authentication that can stop the unauthorized use of cards. This protects businesses from chargeback fees.
With 3DS2, information about the transaction and the customer is securely shared with the bank that issues their card. The bank then confirms whether there’s enough information to authenticate the transaction. It also considers other risk factors, like the shipping location and transaction size.
If anything about the transaction seems potentially fraudulent, 3DS2 adds an authentication challenge. This requires customers to prove their identity by signing into their banking app, entering a code, or using facial or fingerprint recognition. The process is fast and easy, creating minimal friction for the customer.
3. Restrict Access to Payment Information
Data breaches often occur due to internal employees. That can include employees intentionally stealing private information or making simple mistakes that put your business’s security at risk. It’s important to train your employees on best security practices, but you can also limit access to payment information and avoid internal mistakes entirely.
There are many ways you can restrict access to sensitive information. Access tracking allows you to keep logs of employee activity, which you can review in the event of a breach and determine where whose login was involved. You can also use software to restrict and control what apps your employees can access.
4. Use Fraud Monitoring Software
There are various fraud-management systems that can help protect your payment systems from fraud. It’s important to put these in place immediately so they can act as preventative measures. The first system to invest in is a fraud scanning application, which can track customer behavior and flag any suspicious activity.
Vulnerability scanning can look at your system from the outside and determine any potential weak spots that you need to address. Lastly, it’s important to invest in antivirus software that will defend all of the devices related to your business practices from malware.
5. Verify and Validate Transaction Details
You can put systems in place to verify transaction details and help avoid unauthorized purchases. AVS (Address Verification Service) analyzes the billing address of the credit card and the IP address of the buyer. A match implies that the person making the person is a legitimate buyer, while a mismatch could be a sign of fraud.
You can also verify a customer’s identity by requesting their CVV (Card Verification Value). When a customer provides this three-digit code, they confirm that they have the physical card in hand. If they can’t provide the CVV, it may be a sign that they don’t have the physical card and are using stolen credit card numbers.
6. Use Strong Passwords
Passwords are one of your first defenses against hackers. Just like with your personal accounts, you should protect your business accounts with strong passwords. Be sure to set strict password requirements for any employees that interact with your payment system.
A strong password includes:
- A minimum of 7 characters (the more the better)
- No personal information
- A mix of numbers, symbols, and letters
- A mix of upper and lower case letters
- Randomized characters if possible (not real words)
7. Obtain an SSL Certificate
SSL (secure sockets layer) certificates are proof that your business adheres to a protocol for internet security encryption. As we discussed above, encryption allows you to protect customer data by replacing it with unreadable text that is only accessible with a key.
By getting an SSL certificate, you can ensure that you’re using proper encryption methods. It also allows you to showcase your commitment to security to your customers, as it will display a padlock in the address bar of any browser before your website URL. You can get an SSL certification by building your website with a builder that offers it, or by using a payment processor that does it for you.
8. Focus on Compliance
Governing bodies set forth regulations to protect consumer data. You must comply with these rules to avoid any potential legal trouble - plus, the regulations can help you avoid mistakes that could lead to a security breach related to online payments.
The PCI DSS (Payment Card Industry Data Security Standard) covers all of the standards for credit card payments in the US. There are four levels of compliance, with level 1 being the highest level covering the most transactions per year. Pay.com maintains Level 1 PCI DSS compliance so that you don’t have to worry about following the complex set of standards.
There’s also the SCA (Strong Customer Authentication), which is a regulatory requirement in Europe. This requires users who log in and make a purchase to identify themselves using at least two of the three identity factors. This includes something they own, like a mobile device, something they know, like a PIN number, and something they are, like a fingerprint scan.
9. Review Third-Party Vendors
You likely use a few third-party companies to help facilitate your online business. That includes a website host, payment processor, payment gateway service provider, credit card data storage, and more. All of these systems have the potential for a data breach which could allow hackers to steal sensitive payment information.
Review each vendor to confirm that they have strong security measures in place. Each company should adhere to PCI compliance standards and have information about their security standards readily available. You can research them online to see if they’ve had any issues with data breaches in the past.
10. Utilize Software Protection
There are a variety of ways that hackers can try to gain access to your systems. Anytime your business uses the internet, including during the transmission of information for payment, your business is subject to potential threats.
You can put software in place to block these attacks. It’s important to have a designated Wi-Fi network just for your payment system protected by WPA2 (Wi-Fi Protected Access), which is a security protocol just for wireless. You can also set up firewalls to block hackers from gaining access to your payment network.
What's the Most Secure Way for a Business to Accept Payments?
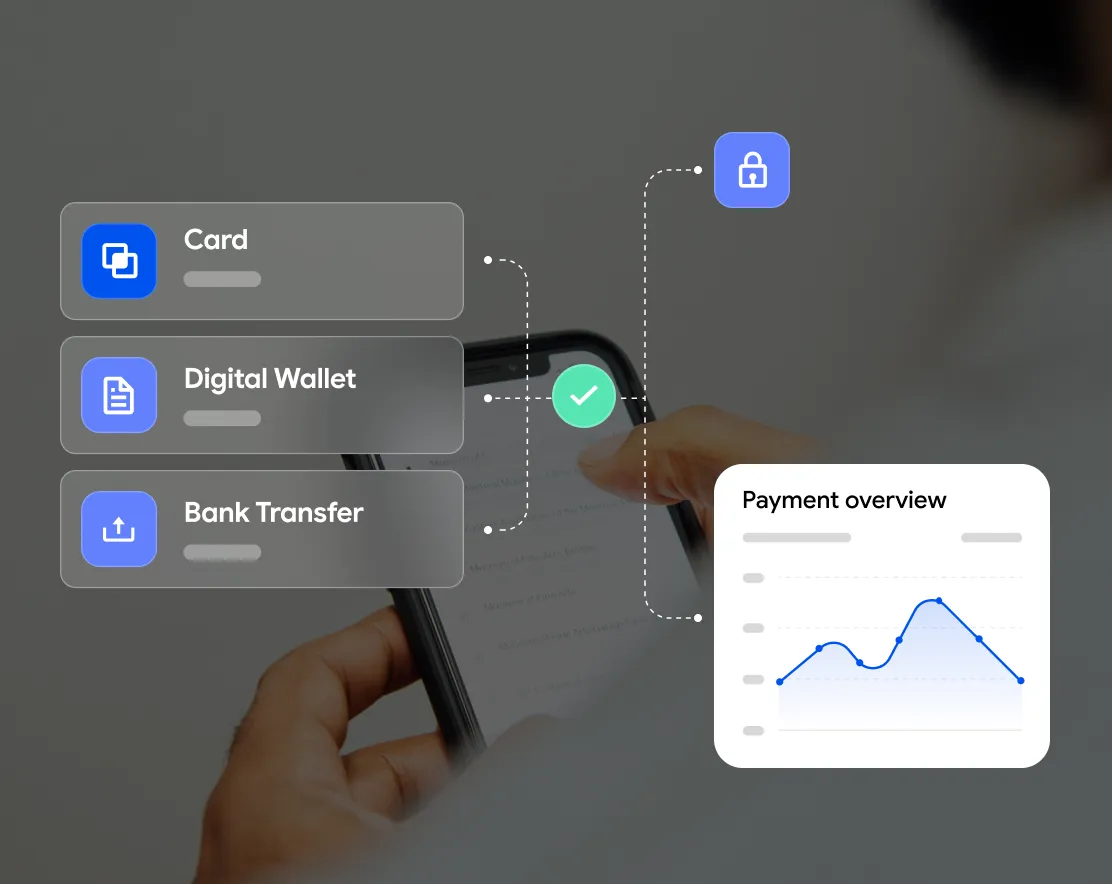
Managing all of your payment security measures and complying with PCI DSS regulations can be a huge drain on your company’s time and financial resources. You could give these tasks to your IT team. Or, you can switch to Pay.com as your payment service provider and rely on our solution to take care of them for you.
The Pay.com system tokenizes all credit card details in transit and provides two-layer authentication by using 3DS2. Pay.com has Level 1 PCI DSS compliance. That’s the highest level of compliance and supports the highest number of transactions per year.
You also get access to extensive reporting via the Pay Dashboard. Review in-depth insights and analytics so you can make informed business decisions. Our developer-friendly APIs allow you to completely customize the checkout page and easily start accepting a variety of payment methods. Plus, Pay.com uses a flat-rate pricing model, so you never deal with unexpected bills.
Click here to create your Pay.com account now!
The Bottom Line
Security is an issue for customers looking to make purchases and businesses that want to increase sales. Ultimately, it’s your job as a merchant to put the proper measures in place to ensure that you provide secure transactions.
You’ll need to take a multi-faceted approach - using defensive strategies, like firewalls, and offensive strategies, like encrypting private information. If you want to take the stress out of secure transactions, make the switch to Pay.com.
We take care of all the security measures so you don’t have to - as well as all the other backend payment activity. With that covered, you can get back to running your business. Click here to get started now!
Pay.com has extensive security measures in place to protect your business from fraudulent transactions. From credit card tokenization and 3DS2 to Level 1 PCI DSS compliance, you can depend on Pay.com for secure transactions every time.


Ginny Dorn is a finance and business copywriter specializing in credit card processing and fintech. She graduated from Western Illinois University with a bachelor's degree in family and consumer sciences.
Get payments insights in your inbox